Antiviruses and hacking go hand in hand. Some might even go as far as saying that the same camps are involved in making both virus and antivirus software and that there is a true conspiracy, a vicious circle that helps sustain both parties in what might be a very lucrative and obscure behind the scene industry. Add government intervention to the mix and you are on the path to being seen as a believer of conspiracy theories, some sort of a whacko.
However derogatory or condescending it is to find yourself in such a position, evidence shows that there might be more to the virus-antivirus ordeal than what meets the eye and that even the most peculiar of these conspiracy theories might in fact be true.
The common narrative of conspiracy, often based on the concept of rivalry, and even more often than not leading to one of the world’s superpowers, be it Russia or the US, it’s a cultural given in today’s world. We are constantly bombarded with news, but more then anything else speculation about what one power is doing to conquer the other. All of these culminating with appropriating a rationale in which we can all understand that the lines between real and fabricated are more blurred than ever before.
Rather than resigning to the idea that there’s nothing we can do about it really, we suggest a different, more empowering kind of approach. The one in which protecting yourself from “the protector” is not something that is unheard of, but rather an a priori condition for true freedom.
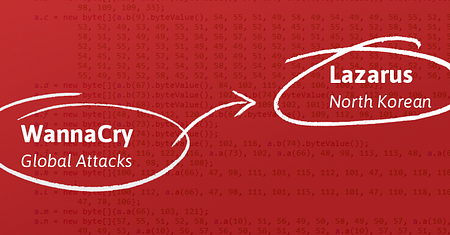
Let’s shed some light on some recent events in the case of cyber espionage between [Russia –US] and [North Korea — South Korea], alleged to have infiltrated malware into antivirus software for the purpose of stealing classified data and military files. The common denominator in both cases? Antivirus tools (Kaspersky for the alleged Russian attach against the States and Hauri in the case of North Korea against South Korea).
However, there are many who argue the validity of these allegations, seen as another PR move amid an alleged American campaign trying to discredit Kaspersky, a premeditate cover up that targeted Kaspersky Labs just because it can detect NSA and CIA’s spying tools. Feeling in more danger at home, having to deal with a pretty robust Surveillance apparatus inside the state, many argue the veracity of it all.
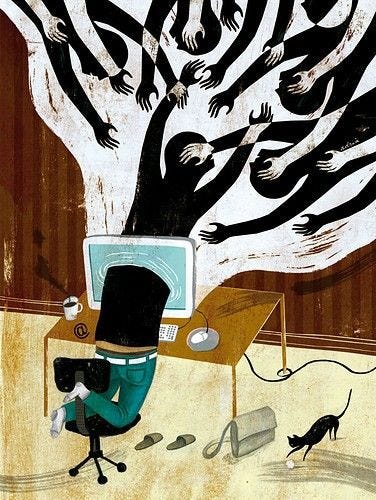
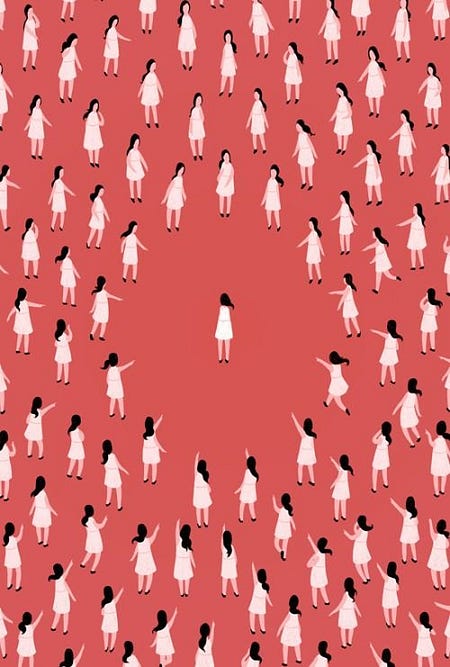
AN AV IS A PANOPTICON BY DESIGN
Beyond the speculation, the two hacking incidents reveal “a troubling truth either way” as observed by Wired. “Antivirus software can pose major risks, whether you’re an intelligence service or an everyday computer user.” states the online mag.
And if we think about the nature of an antivirus, it’s easy to understand why this is. To put it bluntly, an AV is a system-wide omnipotent software. It can track everything and has unrestricted access in order to function, which also make it the perfect bugging device. The utilitarian philosophy of a panopticon (a circular prison with cells arranged around a central well, from which prisoners could at all times be observed) is probably the best comparison.
“AV is pretty much the perfect bugging device on every computer it’s sold on,” says Bobby Kuzma, systems engineer at Core Security. “You’ve got this piece of software that’s in a position to see everything on your computer.”[…]
“We know that the US government has solicited participation from technology vendors in the United States in the past, whether through official channels or more covert mechanisms such as National Security Letters,” says Kuzma. “There’s no reason why other foreign governments cannot compel the same type of cooperation from companies that are based in their territory.”
A VPN TO ENCRYPT ALL YOUR ONLINE DATA, the only way to Zion
Having a robust VPN to encrypt your personal data is nowadays, the only way to Zion.
And as we’re not looking to exhaust the “hide everything I do” reasoning; we mainly believe that a VPN is not paramount to activity that borders on illegal, but the very symbol of our right to the privacy acumen. My IP.io stands for data security and flexibility in the professional VPNunderstanding.
Across the world, businesses use VPNs to connect to remote data centers, or for employees to connect remotely to the physical network of their workplace, while individuals can use VPNs to get access to network resources when they’re not physically on the same LAN (local area network), or as a method for securing and encrypting their information from the potential liabilities that lie ahead once exposed to unsecured networks such as public WiFis or hotspots.
Adding an extra hop to the route between your PC and sites like Facebook, your data location can be easily camouflaged.
REASONS YOU SHOULD START USING A VPN APP. NOW:
· PROTECTS YOUR DATA
your internal data, sites, git repositories, banking credentials and all information will be coated in multiple layers of encryption;
· REMOTE ACCESS
as IT is being challenged to enable safe access to employees remotely by providing mobile VPN, secure email, encrypted containers and virtual desktop infrastructure (VDI), living outside the data security paradigm is simply not smart anymore, whether we’re talking about corporate or personal data;
· IP CAMOUFLAGE
A simple VPN download gets you a new location identity so that you can use geographically dispersed resources;
· BYPASSING FILTERS AND GEORESTRICTIONS
Bypassing Internet censorship in countries where censorship is applied;
· SHARING FILES
You can share files and sensitive information inside a secured group away from prying eyes;
A common misconception goes to say that US VPN services are legally required to log activity on their network. While required to cooperate with US law enforcement, as opposed to other countries, the location of servers is often more important.
LOGGING POLICIES
Not compliant with DMCA are a lot of server locations outside the US.
Very useful when playing online games or logging into services such as banks, Paypal, e-mail providers, etc., a static IP is an underated asset, than not many VPN providers, big names (surprisingly enough), offer.
The ones that do offer a dedicated IP will charge the service as add on and will not always be that transparent about prices.
At My IP.io you can get your own static IP address for as little as $5/ month.
Many times, a dynamic VPN service can be rejected by services like gmail, for example. By using a shared VPN IP, Google may flag your account and require 2factor authentication.
For the record, http://64.233.187.99/ is Google’s.
This is their dedicated IP address and no one else’s, the unique address on the web that has been attached to the domain name google.com.
To have and to hold, a pretty alluring thought!
By Purchasing a Dedicated IP your site is the only one on the Internet that will be using that unique IP address.
Apart from the alluring sound of it, with a dedicated IP address, processes are allowed to run for more than 10 minutes as long as they aren’t consuming too much of the server’s memory, which would result in a CPU throttling. Moreover, certain voice chat programs require a dedicated IP address before they can be setup and used or if you have a program that sends out emails every so many seconds, such as from a mailing list program like DaDa Mail, then you would need to get a dedicated IP address, if it’s going to take more than 10 minutes to send out the emails.
MyIP.io is a self-managed VPN network platform, delivering fast, secure and reliable VPN service , designed with the professional focus in mind. Our platform caters to a wide demographic through three channeled directions:Personal,Dedicated and Business, so it makes for a wonderful choice for corporate or personal use at the same time.
Engineered as a global platform,MyIP.io is a VPN service provider committed to developing applications and services that preserve an open and secure Internet experience while respecting user privacy.
“MyIP.io is the result of the craftsmanship of our engineers, with many years of experience supporting large-scale, custom deployments for businesses , telecommunications companies, multi-service operators and enterprises.” Dave Wilson, CEO My IP.io