Setting yourself up with a reliable, robust VPN service is a real solution to overturn the effects of net neutrality repeal.
Under the new FCC regulation, an ISP has the liberty of charging you more if you watched Netflix instead of Hulu, creating “fast lanes” and unfair advantages to preferred partners. Don’t think your ISP would do that if given the chance? Well, it’s already happening, since net neutrality repeal has gone into effect on June 11th.
With the present “state of affairs” there is no doubt that the online environment is becoming increasingly politicized and the concept of a open but safe internet is in the midst of powerful forces of antagonistic interests fighting each other. A balance between these forces is a desiderate for a healthy environment that we’re not sure how or when we’re going to achieve.
WHAT TO DO?
In the meantime, people are turning to VPNs to preserve access and to reclaim online freedom and privacy and we strongly advice that you do the same.
We tested a few VPN services in terms of speed, security and customer support and MyIP.io stays top of mind. They offer static IPs at no extra costs, have super fast speed for uploads and unparalleled cost to feature ratios.
No longer an exotic tool, VPNs are now entering the mainstream and given the context it’s easy to understand why.
Simply put, when you’re using a VPN, all your data travels through a tunnel encrypted from end to end. In other words, your ISP will not be able to block access or make sense of your data, since you’ll have all your online activity happen elsewhere, not going through your ISP servers and encrypted all the while.
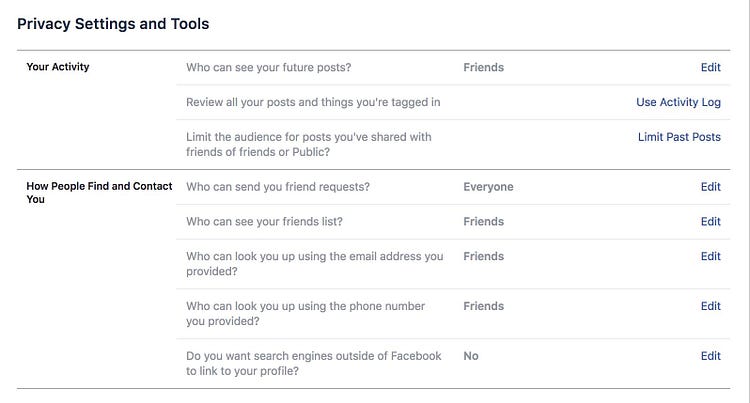
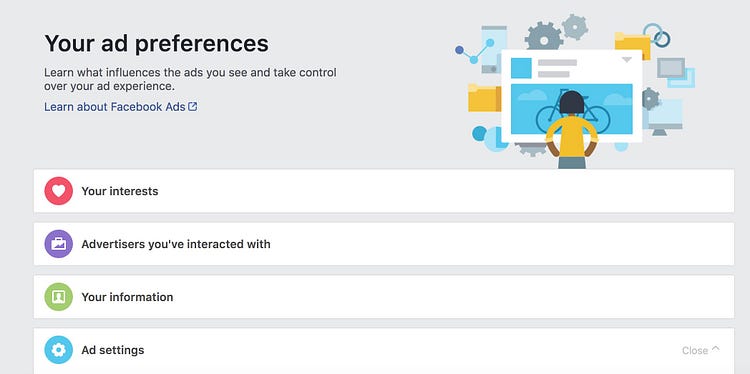
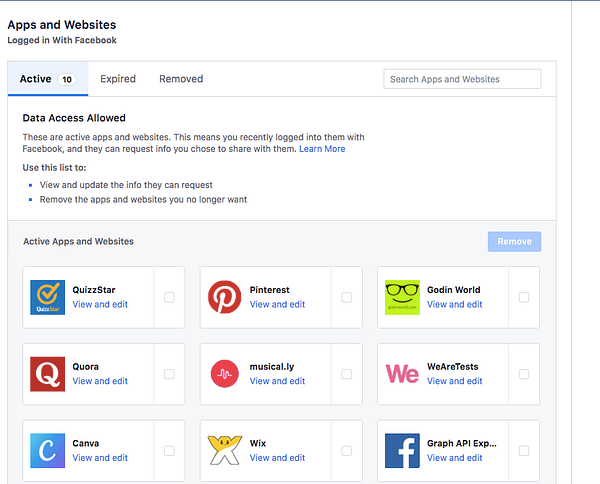
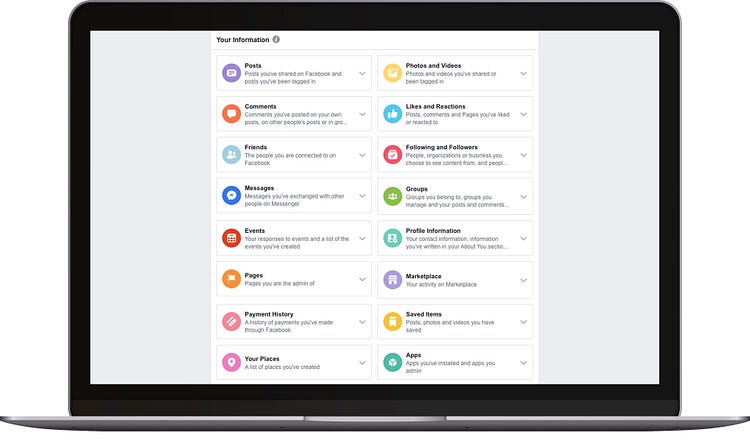
But it’s not just your ISP that keeps track of your browsing data, it’s your cell phone provider too, most apps, operating systems, and other services do the same. Smartphones with preinstalled tracking software, secretly bundled with tracking files are sold everyday, while some companies try to leverage the very problem they created by charging extra for privacy.
Moreover, it’s not just the American net neutrality repeal, UK also passed a bill that basically allows internet history snooping, the infamous bill is known as the Snooper’s Charter (suggestively enough!). This British bill requires that every ISP keeps your search history for 1 full year.
And matters seem to only get worse in the future. Taking hold of your own digital footprint requires savvy, educated users, that know their rights and are not willing to compromise when it comes to their own privacy.
It’s easy to understand why more and more people resort to using a VPN service, rather than letting their information “fly” to unknown servers where they can be stored indefinitely.
An exact break down of all the things you can use a VPN for would maybe further clarify this topic.
We listed the most popular ones we could think of:
1. Torrents
Torrents are not all illegal, but for an ISP is really difficult to set the legal ones from the illicit, so very often that not they block this kind of activity. Having a VPN in place will camouflage the subject of your downloads and will make it harder for your ISP to track and block torrenting.
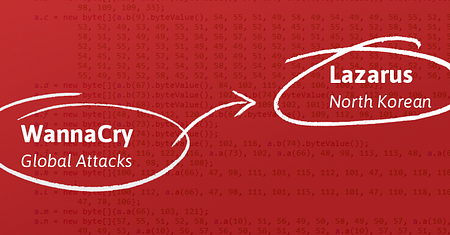
2. Security
Think of your health records, your banking details and other sensitive information that you might use while online. A VPN will encrypt that information and will keep your connection secure at all times.
3.Geo-restricted content
Every time you travel you get a different set of content according to your location. Sticking to your country of residence through a VPN while outside the country will leave your content unchanged, like say your Netflix catalog. On the other hand, changing your IP location to one that allows you to watch the World Cup in Russia as it happens is also a VPN away.
4. Research or journalism
Research data or revealing a sensitive issue to the public through journalism is something that people might strive extra to acquire access to. Having that data encrypted through the help of a VPN will spare you the trouble.
5. VOIP services
Using services like Skype or FaceTime to interact to your peers at work, may be a common thing inside your company. VOIP security is still lagging behind, but a VPN will help secure your connections, so you don’t have to.
6. Public Wi-Fi in airports or coffee shop
Notorious for welcoming prying eyes, airports and public Wi-Fi spots are not to be used sans VPN protection.
8. Gaming
Your connection to your gaming comrades can be direct through a VPN, resulting in increased load times and limited buffer overflows. You will also be able to get the latest releases of your favorite games as they happen and not wait for them to hit your location upon schedule.
10. Checking your competition out
It’s pretty easy for anyone to track the source of their traffic through their Analytics account so you too can be spotted checking your competition out. You can still do that undisturbed and anonymous with the help of a VPN service.
Having a VPN in place is the smart approach to getting around all this. Think at a VPN as the middleman between you and the internet, where your ISP can only see a bunch of encrypted traffic. And since your VPN knows as much as your ISP would, it’s very important to choose a reliable one with a zero log policy and a strong encryption.
Services like MyIP.io will offer you a self-managed VPN platform, delivering fast, secure and reliable VPN service . This platform caters to a wide demographic through three channeled directions: Personal, Dedicated and Business, so it makes for a wonderful choice for corporate or personal use at the same time. Whatever provider you may chose, remember that the smart approach is to use a VPN service that you feel is the best match for you. Until then, stay smart, use a VPN!